Red Hot Cyber - Notizie su Cybercrime e Sicurezza Informatica
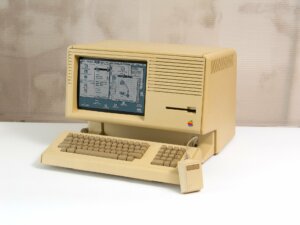
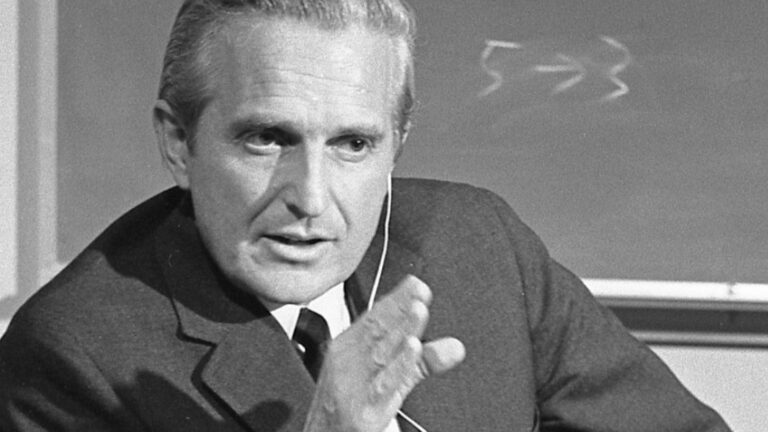
Oggi nasceva Douglas Engelbart: l’uomo che ha visto e inventato il futuro digitale
Certe volte, pensandoci bene, uno si chiede come facciamo a dare per scontato il mondo che ci circonda. Tipo, clicchiamo, scorriamo, digitiamo, e tutto sembra così naturale, quasi fosse sempre stato q...
L’IA non chiede il permesso: sta riscrivendo le regole in fretta e probabilmente male
L’intelligenza artificiale è entrata nel lavoro senza bussare. Non come una rivoluzione urlata, ma come una presenza costante, quasi banale a forza di ripetersi. Ha cambiato il modo in cui le persone ...
Attenzione al “I am not a robot”: la trappola malware che usa Google Calendar
Una nuova minaccia si aggira, usando la nostra più grande debolezza: l’abitudine. Quante volte, infatti, capita di ritrovarsi a cliccare su caselle di verifica senza pensarci due volte? Ora, pare che ...
WinRAR come arma: Google scopre una falla sfruttata da APT e cybercriminali
La falla di sicurezza in WinRAR, emersa durante la scorsa estate, ha mostrato una diffusione maggiore rispetto alle aspettative. Diverse organizzazioni, sia criminali comuni che gruppi APT finanziati ...
Colpo al cuore del cybercrime: RAMP messo offline. Il “tempio” del ransomware cade!
Il forum RAMP (Russian Anonymous Marketplace), uno dei principali punti di riferimento del cybercrime underground internazionale, è stato ufficialmente chiuso e sequestrato dalle forze dell’ordine sta...
La privacy è morta? No, ma è in coma! Cosa celebriamo davvero oggi 28 gennaio
Oggi è il 28 gennaio e, come ogni anno da un bel po’ di tempo a questa parte, ci ritroviamo a celebrare la Giornata europea della protezione dei dati. È una roba che nasce nel 2006, o giù di lì, per r...
OpenSSL: 12 bug di sicurezza rilevati tra i quali una vulnerabilità critica
Un aggiornamento di sicurezza è stato rilasciato dai responsabili della manutenzione di OpenSSL, la libreria crittografica, al fine di risolvere circa una dozzina di vulnerabilità che includono, tra g...
Autonomia Digitale: La Francia dice addio a Teams e Zoom dal 2027
Non è la prima iniziativa che spunta su questo fronte, ultimamente. Anzi, se ne sentono diverse, una dopo l’altra. Ed è quasi inevitabile: autonomia tecnologica e sicurezza nazionale stanno diventando...
Il ransomware non blocca i server, blocca il credito. Il lato finanziario della cybersecurity
C’è questa idea sbagliata, un po’ romantica volendo, per cui il ransomware è “roba da IT”: qualche server in crisi, due notti in bianco, poi si riparte e fine… La realtà, soprattutto per un’azienda qu...
Difesa attiva e hack back: il labirinto legale della cybersecurity
Nel precedente contributo abbiamo esplorato come la posizione di garanzia del professionista della cybersecurity si scontri con fattispecie classiche come l’accesso abusivo. Tuttavia, nella mia esperi...
Articoli più letti dei nostri esperti
Oggi nasceva Douglas Engelbart: l’uomo che ha visto e inventato il futuro digitale
Massimiliano Brolli - 30 Gennaio 2026
BitLocker sotto accusa: Microsoft ammette di consegnare le chiavi di cifratura all’FBI
Redazione RHC - 29 Gennaio 2026
FRANCE TRAVAIL, multa da 5 milioni per violazione dati personali
Redazione RHC - 29 Gennaio 2026
WhatsApp cambia pelle: Arriva la modalità “Paranoia” (e no, non è per tutti)
Silvia Felici - 29 Gennaio 2026
Il CISA ci insegna come farsi un Data Leak da soli, senza nemmeno assoldare un hacker
Redazione RHC - 29 Gennaio 2026
Smartphone in affitto a tua insaputa: Google smantella una rete proxy globale
Bajram Zeqiri - 29 Gennaio 2026
L’IA non chiede il permesso: sta riscrivendo le regole in fretta e probabilmente male
Massimiliano Brolli - 29 Gennaio 2026
Attenzione al “I am not a robot”: la trappola malware che usa Google Calendar
Bajram Zeqiri - 29 Gennaio 2026
WinRAR come arma: Google scopre una falla sfruttata da APT e cybercriminali
Bajram Zeqiri - 29 Gennaio 2026
Nike indaga su un presunto attacco hacker: “Sottratti 1,4 TB di dati”
Pietro Melillo - 29 Gennaio 2026
Ultime news
Oggi nasceva Douglas Engelbart: l’uomo che ha visto e inventato il futuro digitale
BitLocker sotto accusa: Microsoft ammette di consegnare le chiavi di cifratura all’FBI
FRANCE TRAVAIL, multa da 5 milioni per violazione dati personali
WhatsApp cambia pelle: Arriva la modalità “Paranoia” (e no, non è per tutti)
Il CISA ci insegna come farsi un Data Leak da soli, senza nemmeno assoldare un hacker
Smartphone in affitto a tua insaputa: Google smantella una rete proxy globale
Scopri le ultime CVE critiche emesse e resta aggiornato sulle vulnerabilità più recenti. Oppure cerca una specifica CVE
Ricorrenze storiche dal mondo dell'informatica
Articoli in evidenza
 Cultura
CulturaCerte volte, pensandoci bene, uno si chiede come facciamo a dare per scontato il mondo che ci circonda. Tipo, clicchiamo, scorriamo, digitiamo, e tutto sembra così naturale, quasi fosse sempre stato qui. E invece no,…
 Innovazione
InnovazioneL’intelligenza artificiale è entrata nel lavoro senza bussare. Non come una rivoluzione urlata, ma come una presenza costante, quasi banale a forza di ripetersi. Ha cambiato il modo in cui le persone lavorano, sì, ma…
 Cybercrime
CybercrimeUna nuova minaccia si aggira, usando la nostra più grande debolezza: l’abitudine. Quante volte, infatti, capita di ritrovarsi a cliccare su caselle di verifica senza pensarci due volte? Ora, pare che i malintenzionati abbiano creato…
 Cybercrime
CybercrimeLa falla di sicurezza in WinRAR, emersa durante la scorsa estate, ha mostrato una diffusione maggiore rispetto alle aspettative. Diverse organizzazioni, sia criminali comuni che gruppi APT finanziati da nazioni, stanno sfruttando attivamente questa vulnerabilità,…
 Cybercrime
CybercrimeIl forum RAMP (Russian Anonymous Marketplace), uno dei principali punti di riferimento del cybercrime underground internazionale, è stato ufficialmente chiuso e sequestrato dalle forze dell’ordine statunitensi. La notizia è emersa dopo che il dominio associato…