Attackers are actively exploiting a critical privilege escalation vulnerability in the WordPress Motors theme, allowing them to hijack administrator accounts and take complete control of the target site.
The malicious activity was discovered by Wordfence, which last month reported a critical vulnerability, the CVE-2025-4322, which affects all versions of the Motors theme up to 5.6.67. This theme, developed by StylemixThemes, has 22,460 sales on Envato Market and is very popular among owners of automotive-related websites.
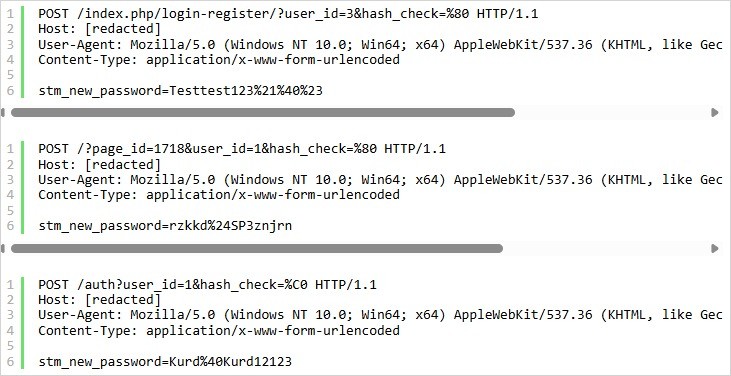
The issue is related to the Login Register widget and the incorrect validation of the user’s identity when updating a password, which allows unauthenticated attackers to change administrator passwords. Therefore, to exploit the bug, an attacker must first find the URL where the widget is located by checking /login-register, /account, /reset-password, /signin, etc. using special POST requests. Such requests contain invalid UTF-8 characters in the hash_check value, which leads to incorrect hash comparisons when resetting a password.
The POST body contains the stm_new_password value, which resets the user’s password based on IDs that typically belong to site administrators.
In May, StylemixThemes developers released version 5.6.68, which fixed CVE-2025-4322, but many users had not yet installed the updates and may now be vulnerable to attacks.
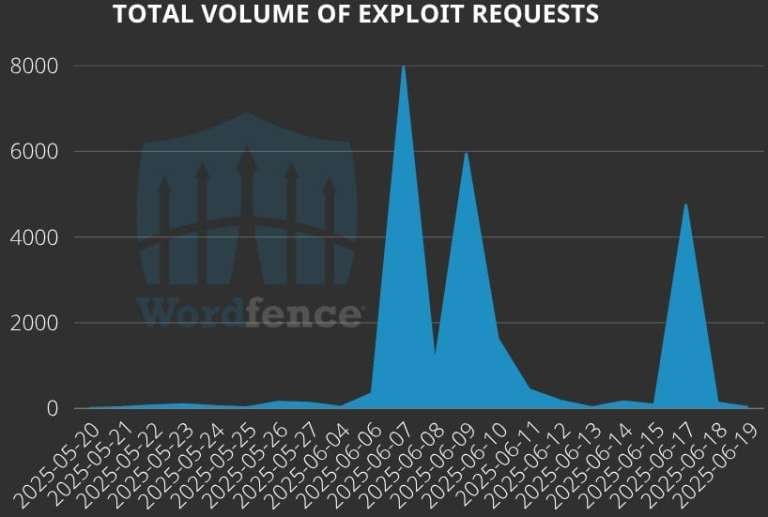
Wordfence analysts reported that attacks on the new vulnerability began as early as May 20, just one day after the issue was disclosed. More extensive attacks began after June 7, 2025, and Wordfence says it has already blocked over 23,100 hacking attempts against its customers.
According to experts, the passwords used by attackers in the attacks include:
Once access is gained, attackers log into the WordPress dashboard as administrators and create additional administrative accounts to gain a foothold on the hacked resource. Experts write that the sudden appearance of such accounts, combined with the locking of existing administrator accounts (passwords no longer working), is a sure sign of CVE-2025-4322 exploitation. Motors users are advised to update their theme as soon as possible.