
Group-IB specialists have recorded new attacks by the Bloody Wolf hacker group, which has been targeting Kyrgyzstan since June 2025 and has expanded its operations to Uzbekistan since October. The financial sector, government agencies, and IT companies are at risk.
According to researchers, the attackers are impersonating the Kyrgyz Ministry of Justice, using fake PDF documents and seemingly legitimate domains, but are actually distributing Java archives (JARs) containing the NetSupport RAT malware.
Bloody Wolf has been active since at least the end of 2023. Previously, the group targeted Kazakhstan and Russia, distributing STRRAT and NetSupport via phishing attacks. The group’s geographic reach has now expanded to Central Asia, but its tactics remain the same: in emails, the group impersonates government officials, attempting to trick victims into opening malicious attachments.
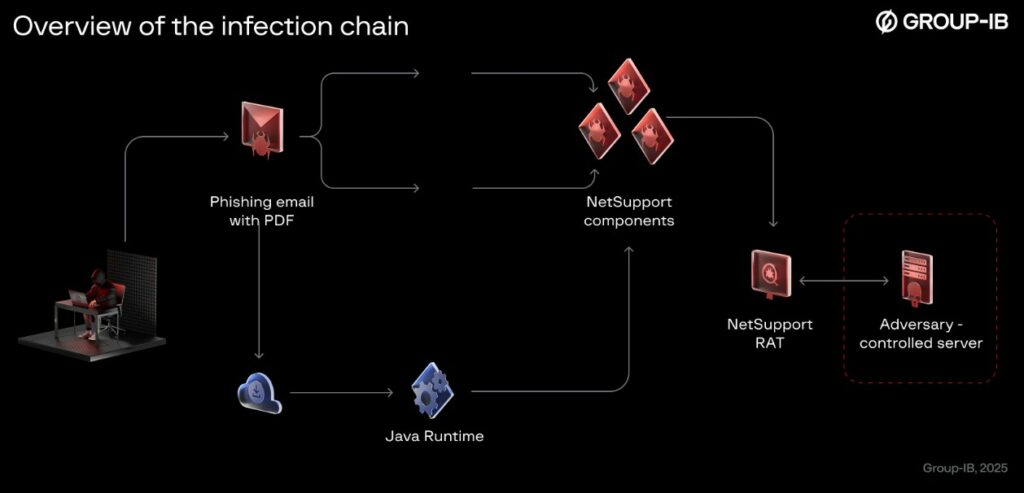
The attack scheme is simple. The victim receives an email containing a link to a seemingly important document. Clicking the link downloads a JAR file along with instructions for installing Java Runtime. The email claims that Java is required to view the files, but in reality, the downloader downloads NetSupport RAT from the hacker’s server and installs itself on the system in three ways: via a scheduled task, a registry entry in the Windows registry, and a BAT file in the startup folder.
Experts write that during the attacks on Uzbek organizations, hackers used geofencing : if a request came from outside Uzbekistan, the victim was redirected to the legitimate website data.egov.uz. However, requests from within the country triggered the download of a JAR file from a link embedded in a PDF.
Note that all of the group’s JAR downloaders are compiled using an older version of Java 8 (released in March 2014). Experts believe the group has its own generator or template for creating these files. Furthermore, the version of the NetSupport malware is also far from recent, dating back to October 2013.
The researchers conclude that Bloody Wolf demonstrates that even inexpensive commercial tools can be transformed into effective weapons for targeted and sophisticated attacks.
Follow us on Google News to receive daily updates on cybersecurity. Contact us if you would like to report news, insights or content for publication.
