Author: Andrea Nicelli, Head of Italy and Spain at Resilience Italy’s critical infrastructure is highly exposed to cyber threats, ranking fourth in the world and first in Europe for number...
Discover the Magic of Programming Through the Charm of Mathematics: A Journey of Growth and Learning Good morning everyone, I’m Davide Cavallini, Senior Programmer and Penetration Tester This article was written...
Giorgio sat in the self-help circle, the dim candlelight dancing on the walls. The eyes of the other participants were fixed on him, waiting for him to speak. It was...
Author: Carlo DenzaOriginal Publication Date: 07/10/2021Translator: Tara Lie Star Trek IV - The Voyage Home, directed by Leonard Nimoy (USA, 1986, Paramount Pictures): “The starship ‘U.S.S. Enterprise NCC-1701’ and its...
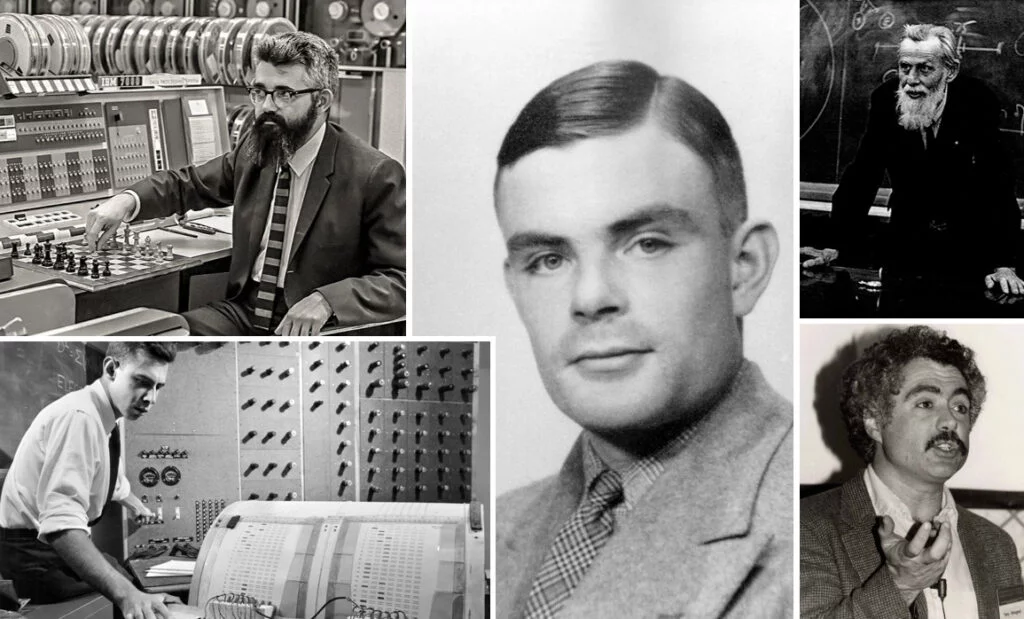
Author: Massimiliano BrolliOriginal Publication Date: 19/03/2021Translator: Tara Lie Hacker culture was brought to life thanks to computer scientist Richard Greenblatt and mathematician Bill Gosper at the Massachusetts Institute of Technology (MIT). It...