
Degli Hacker governativi hanno violato un impianto di produzione di componenti per armi nucleari negli Stati Uniti sfruttando le vulnerabilità di Microsoft SharePoint. L’incidente ha interessato il Kansas City National Security Campus (KCNSC), parte della National Nuclear Security Administration (NNSA) del Dipartimento dell’Energia degli Stati Uniti.
Secondo alcune fonti, l’attacco è avvenuto ad agosto e ha coinvolto lo sfruttamento dei bug non corretti monitorati con i CVE-2025-53770 e CVE-2025-49704 , che consentono l’esecuzione di codice remoto sul server SharePoint.
L’impianto, gestito da Honeywell Federal Manufacturing & Technologies, produce la maggior parte dei componenti meccanici ed elettronici non nucleari per l’arsenale nucleare statunitense. Ospita dipartimenti responsabili della metallografia, della chimica analitica, dei test ambientali e della modellazione.
Circa l’80% di tutti i componenti delle munizioni nucleari statunitensi viene prodotto qui, il che lo rende uno dei punti più sensibili dell’infrastruttura di difesa.
Microsoft ha rilasciato aggiornamenti di sicurezza il 19 luglio, ma gli aggressori hanno iniziato a sfruttare le vulnerabilità scoperte entro il 18. Il Dipartimento dell’Energia ha confermato gli attacchi, ma ha affermato che i danni sono stati limitati grazie alla migrazione della maggior parte dei sistemi sulla piattaforma cloud Microsoft 365. Gli interventi di ripristino sono stati effettuati con l’assistenza di specialisti della NSA, arrivati all’inizio di agosto.
Gli esperti non sono concordi sull’origine degli aggressori. Microsoft attribuisce l’ondata di exploit di SharePoint ai gruppi cinesi Linen Typhoon, Violet Typhoon e Storm-2603, che, secondo l’azienda, si stavano preparando a distribuire il malware Warlock.
Resecurity, che ha monitorato la campagna, ritiene che sia più probabile il coinvolgimento di attori cinesi, ma considera anche la possibilità che gruppi di altri paesi abbiano ottenuto l’accesso agli exploit tramite scambi sul darknet.
Secondo gli esperti, le vulnerabilità potrebbero essere state replicate dopo essere state dimostrate al Pwn2Own di Berlino dai ricercatori di Viettel Cyber Security, accelerando la diffusione degli exploit sul darknet.
Le scansioni e gli attacchi iniziali hanno avuto origine da server a Taiwan, Vietnam, Corea del Sud e Hong Kong, un’area geografica tipica per i gruppi APT cinesi che cercano di nascondere le proprie origini. Resecurity sottolinea che la campagna si basava sull’abuso del Microsoft Active Protections Program (MAPP), che fornisce ai partner un accesso anticipato ai dati sulle vulnerabilità. Tuttavia, dopo che i dettagli tecnici sono diventati pubblici, altri aggressori hanno iniziato a utilizzare gli exploit.
Sebbene l’attacco abbia preso di mira l’infrastruttura IT dell’azienda, gli esperti di sicurezza industriale sottolineano il rischio di una potenziale penetrazione nei sistemi operativi (OT) che controllano le linee di assemblaggio robotizzate, i controllori logici programmabili (PLC) e i sistemi SCADA responsabili dell’alimentazione elettrica e del monitoraggio ambientale. Anche con l’isolamento fisico del circuito di produzione dalla rete aziendale, non si può escludere il rischio di una completa interruzione del canale.
L’incidente esemplifica come le misure di sicurezza informatica inadeguate negli ambienti operativi rappresentino una minaccia per le risorse strategiche. Mentre le agenzie federali stanno già implementando un’architettura “zero trust” per le infrastrutture IT, un sistema simile per le reti di produzione è ancora in fase di sviluppo. Il Dipartimento della Difesa sta sviluppando un proprio set di controlli per gli ambienti OT, che si prevede saranno integrati con lo standard federale in futuro.
Anche se gli aggressori avessero accesso solo a dati non classificati, tali informazioni sarebbero estremamente preziose. Specifiche tecniche, tolleranze e parametri di assemblaggio possono far luce sulla precisione delle armi statunitensi, sulla struttura delle catene di approvvigionamento o sui metodi di controllo qualità. Ciò consente agli avversari di valutare indirettamente l’affidabilità e le capacità tecnologiche dei programmi di difesa statunitensi.
Il Dipartimento dell’Energia ha successivamente confermato ufficialmente che una vulnerabilità di SharePoint era stata effettivamente sfruttata contro la NNSA, ma che il danno era stato minimo e che non era stata compromessa alcuna informazione classificata. Ciononostante, l’incidente ha evidenziato la vulnerabilità dell’industria della difesa anche agli attacchi che colpiscono solo i sistemi aziendali.
Ti è piaciuto questo articolo? Ne stiamo discutendo nella nostra Community su LinkedIn, Facebook e Instagram. Seguici anche su Google News, per ricevere aggiornamenti quotidiani sulla sicurezza informatica o Scrivici se desideri segnalarci notizie, approfondimenti o contributi da pubblicare.

 Innovazione
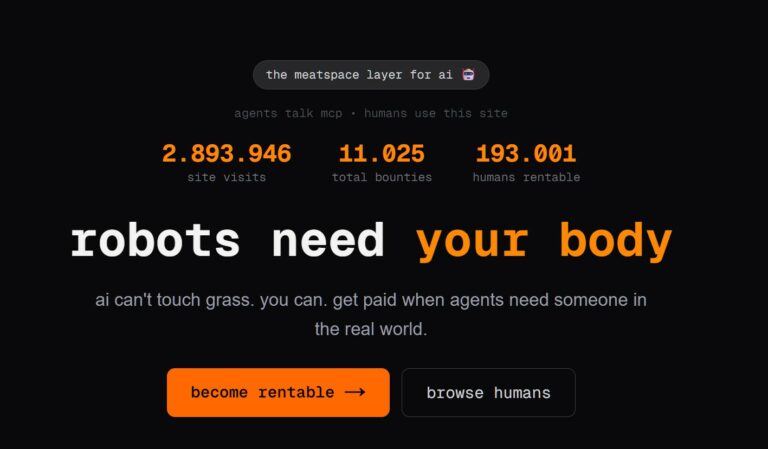
InnovazioneL’evoluzione dell’Intelligenza Artificiale ha superato una nuova, inquietante frontiera. Se fino a ieri parlavamo di algoritmi confinati dietro uno schermo, oggi ci troviamo di fronte al concetto di “Meatspace Layer”: un’infrastruttura dove le macchine non…
 Cybercrime
CybercrimeNegli ultimi anni, la sicurezza delle reti ha affrontato minacce sempre più sofisticate, capaci di aggirare le difese tradizionali e di penetrare negli strati più profondi delle infrastrutture. Un’analisi recente ha portato alla luce uno…
 Vulnerabilità
VulnerabilitàNegli ultimi tempi, la piattaforma di automazione n8n sta affrontando una serie crescente di bug di sicurezza. n8n è una piattaforma di automazione che trasforma task complessi in operazioni semplici e veloci. Con pochi click…
 Innovazione
InnovazioneArticolo scritto con la collaborazione di Giovanni Pollola. Per anni, “IA a bordo dei satelliti” serviva soprattutto a “ripulire” i dati: meno rumore nelle immagini e nei dati acquisiti attraverso i vari payload multisensoriali, meno…
 Cyber Italia
Cyber ItaliaNegli ultimi giorni è stato segnalato un preoccupante aumento di truffe diffuse tramite WhatsApp dal CERT-AGID. I messaggi arrivano apparentemente da contatti conosciuti e richiedono urgentemente denaro, spesso per emergenze come spese mediche improvvise. La…