
Un’allerta globale è stata lanciata dalla Cybersecurity and Infrastructure Security Agency (CISA) degli Stati Uniti, riguardante lo sfruttamento attivo di una falla critica di esecuzione di codice remoto (RCE) nel servizio di aggiornamento dei server Windows (WSUS) di Microsoft, rivolta a tutte le organizzazioni mondiali.
La vulnerabilità, catalogata come CVE-2025-59287, presenta un punteggio CVSS pari a 9,8, permettendo a malintenzionati senza autenticazione di eseguire codice a con diritti di amministratore all’interno di una rete, minacciando così le organizzazioni.
La falla di sicurezza, originata dalla deserializzazione all’interno di WSUS, ha subito una parziale correzione mediante la patch mensile Microsoft di ottobre, tuttavia si è reso necessario un aggiornamento straordinario pubblicato il 23 ottobre 2025, a causa dell’insufficienza della soluzione iniziale.
Microsoft e CISA esortano a un intervento urgente per contrastare la minaccia. Per iniziare, occorre individuare i server suscettibili a rischio eseguendo una scansione per rilevare quelli con il ruolo WSUS attivo e con le porte 8530/8531 aperte. Applicare immediatamente la patch out-of-band del 23 ottobre , quindi riavviare per garantire la mitigazione completa. Ritardare questa operazione potrebbe esporre le reti a RCE non autenticate.
Per coloro che non possono applicare subito la patch, le soluzioni temporanee includono la disabilitazione del ruolo WSUS o il blocco del traffico in ingresso verso le porte interessate sul firewall host; queste azioni non devono essere annullate finché non viene installato l’aggiornamento.
Pochi giorni prima, il ricercatore Batuhan Er di HawkTrace aveva rilasciato exploit proof-of-concept (PoC) che hanno velocizzato l’attività malevola, permettendo agli attaccanti di bersagliare i server WSUS in esecuzione con un account SYSTEM.
La società di sicurezza olandese Eye Security ha identificato i primi tentativi di sfruttamento della vulnerabilità alle 06:55 UTC del 24 ottobre 2025, mediante un payload .NET codificato in Base64.
Tale payload è stato progettato per superare i sistemi di registrazione attraverso l’esecuzione di comandi veicolati da un’intestazione di richiesta personalizzata denominata “aaaa”. La minaccia, secondo quanto riportato dalle aziende specializzate in sicurezza, sta aumentando rapidamente, con segnalazioni di attacchi reali già a partire dal 24 ottobre 2025.
La CISA, inoltre, ha incluso il CVE-2025-59287 nel suo catalogo delle vulnerabilità sfruttate (KEV), impone alle agenzie federali di risolvere la vulnerabilità entro il 14 novembre 2025, data che evidenzia la facile sfruttabilità e la scarsa complessità dell’exploit, il quale non necessita di interazione o autenticazione utente.
Le aziende che utilizzano WSUS per la gestione centralizzata degli aggiornamenti sono esposte a notevoli rischi, in quanto una violazione efficace potrebbe permettere agli aggressori di diffondere aggiornamenti dannosi su tutti i dispositivi collegati.
La vulnerabilità sfrutta un meccanismo di serializzazione legacy nell’endpoint GetCookie(), in cui gli oggetti AuthorizationCookie crittografati vengono decrittografati tramite AES-128-CBC e deserializzati tramite BinaryFormatter senza convalida del tipo, aprendo la porta al controllo completo del sistema.
Ti è piaciuto questo articolo? Ne stiamo discutendo nella nostra Community su LinkedIn, Facebook e Instagram. Seguici anche su Google News, per ricevere aggiornamenti quotidiani sulla sicurezza informatica o Scrivici se desideri segnalarci notizie, approfondimenti o contributi da pubblicare.

 Innovazione
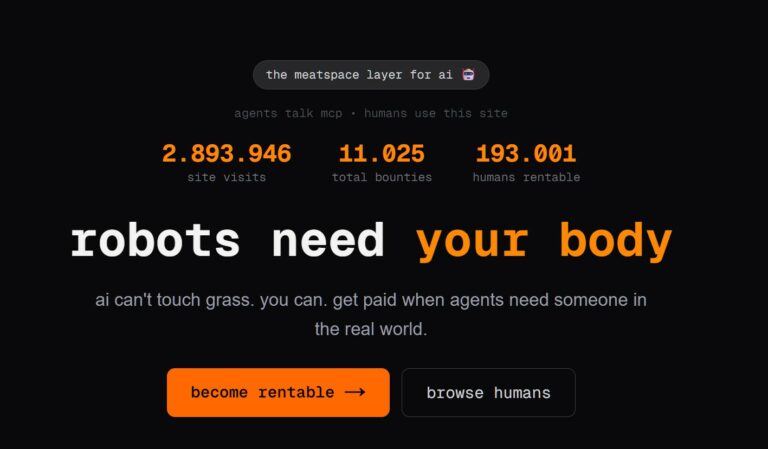
InnovazioneL’evoluzione dell’Intelligenza Artificiale ha superato una nuova, inquietante frontiera. Se fino a ieri parlavamo di algoritmi confinati dietro uno schermo, oggi ci troviamo di fronte al concetto di “Meatspace Layer”: un’infrastruttura dove le macchine non…
 Cybercrime
CybercrimeNegli ultimi anni, la sicurezza delle reti ha affrontato minacce sempre più sofisticate, capaci di aggirare le difese tradizionali e di penetrare negli strati più profondi delle infrastrutture. Un’analisi recente ha portato alla luce uno…
 Vulnerabilità
VulnerabilitàNegli ultimi tempi, la piattaforma di automazione n8n sta affrontando una serie crescente di bug di sicurezza. n8n è una piattaforma di automazione che trasforma task complessi in operazioni semplici e veloci. Con pochi click…
 Innovazione
InnovazioneArticolo scritto con la collaborazione di Giovanni Pollola. Per anni, “IA a bordo dei satelliti” serviva soprattutto a “ripulire” i dati: meno rumore nelle immagini e nei dati acquisiti attraverso i vari payload multisensoriali, meno…
 Cyber Italia
Cyber ItaliaNegli ultimi giorni è stato segnalato un preoccupante aumento di truffe diffuse tramite WhatsApp dal CERT-AGID. I messaggi arrivano apparentemente da contatti conosciuti e richiedono urgentemente denaro, spesso per emergenze come spese mediche improvvise. La…