
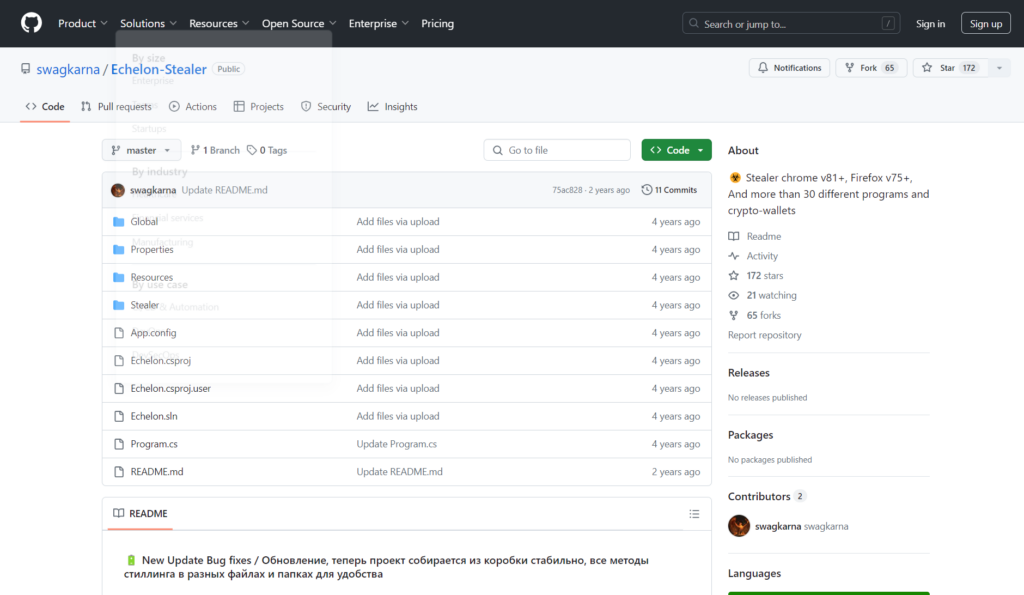
Echelon Stealer is an infostealer malware that was first discovered in 2018 and is still active. Currently shared as an open-source tool on GitHub, Echelon Stealer offers various advanced features for extracting sensitive data.
Despite being presented as an educational project, its potential for malicious use is significant.
An infostealer is a type of malware specifically designed to steal sensitive information from infected devices. These malware can gather a wide range of data, including:
Infostealers are often distributed through phishing campaigns, malicious email attachments, compromised software downloads, and other social engineering techniques. Once installed, the infostealer collects data and sends it to a server controlled by the attackers, allowing them to exploit this information for various illicit purposes, such as identity theft, financial fraud, and unauthorized access to systems and networks.
Echelon Stealer can extract data from various browsers and applications. Supported browsers include all Chromium-based ones, Edge, and Gecko-based (such as Mozilla Firefox). The extraction features include:
Echelon Stealer can also gather data from various VPN applications and cryptocurrency wallets, including:
In addition to data collection capabilities, Echelon Stealer includes other functionalities such as:
The latest project update includes various bug fixes and has made the project more stable. Now, all extraction methods are organized into different files and folders for greater convenience.
The creator of Echelon Stealer has clearly stated that the project is written exclusively for educational purposes and assumes no responsibility for the use of the project or any of its code parts. This notice is essential as the misuse of such tools can lead to severe legal and ethical consequences.
Echelon Stealer represents an example of how open-source tools can be used for both legitimate and malicious purposes. It is crucial that such tools are used with awareness and responsibility. The community of developers and security researchers must remain vigilant and collaborative to mitigate the risks associated with these tools and promote the ethical use of technology.
