
Industrial Control Systems (ICS), critical to the operation of critical infrastructure such as power, water and transportation networks, are increasingly vulnerable to cyberattacks. In this context, the article HoneyPLC: A Next-Generation Honeypot for Industrial Control Systemse proposes an advanced and scalable honeypot designed to simulate real PLCs (programmable logic controllers) and automatically collect malware, in particular malicious code written in ladder logic, significantly improving the state of the art in ICS protection.
Unlike traditional honeypots, HoneyPLC stands out in three key ways: high interactivity, large scalability, and deception capabilities. It can faithfully emulate industrial network protocols, providing interaction similar to that of a real PLC.
It can also simulate multiple PLC models from different brands, making it much more adaptable than previous honeypots, which typically only support one or two models. Its modular structure also allows you to create custom profiles for different industrial devices.
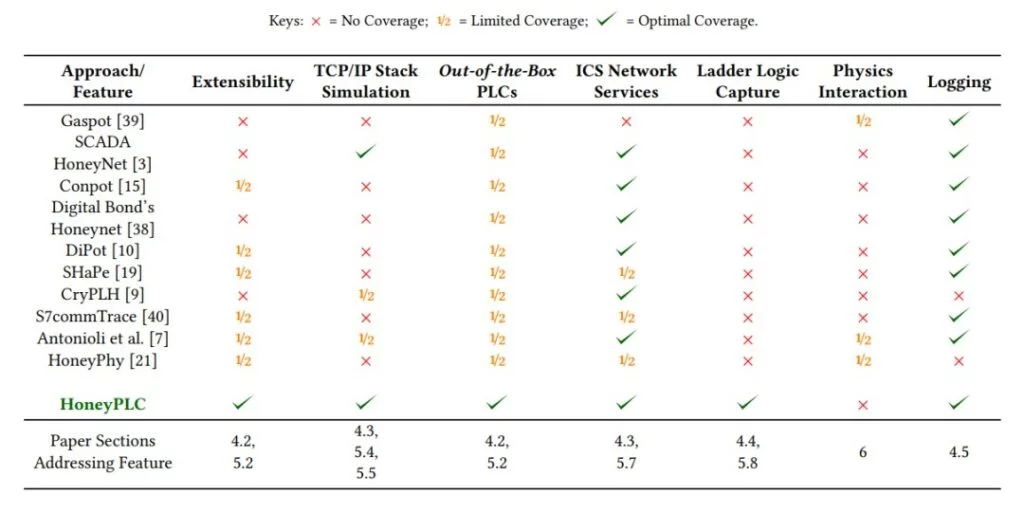
One of the most innovative aspects is the ability to hide: HoneyPLC can fool the most common reconnaissance tools, such as Nmap, by providing plausible answers thanks to the automatic generation of fingerprints and accurate emulation of protocols. Furthermore, every attacker interaction is tracked and logged, with the ability to collect ladder logic programs injected into memory blocks in real time, a feature that was missing in previous ICS honeypots.
The experimental evaluation involved five real PLC models (including Siemens, Allen-Bradley and ABB) and demonstrated that HoneyPLC is able to faithfully replicate the behavior of each of them. It also survived scans from reconnaissance tools by simulating network stacks consistent with the target devices. It also successfully captured malware written in ladder logic, confirming its usefulness as a malicious code collection and analysis tool.
In conclusion, HoneyPLC represents a major step forward in industrial system protection. With its ability to scale across multiple PLC models, simulate realistic interactions, and collect malware in an automated manner, it is a powerful tool for ICS security research and for creating increasingly effective countermeasures against industrial cyber threats.
