
Negli ultimi mesi, come anticipato più volte su Red Hot Cyber, è emerso un nuovo fronte nello scenario del phishing aziendale: attacchi tramite Microsoft Teams in cui i malintenzionati si spacciano per personale IT o help desk. Approfittando delle funzionalità base della piattaforma, come la comunicazione esterna consentita per default, gli aggressori ingaggiano gli utenti con messaggi, chiamate o richieste di condivisione schermo, spesso inserendosi in modo insospettabile nella chat di Teams. L’efficacia di queste tattiche è cresciuta parallelamente all’adozione diffusa di Teams come strumento primario di lavoro collaborativo.
I danni possono concretizzarsi quando la vittima, convinta di aiutare un tecnico interno, accede alla condivisione o all’uso di strumenti di controllo remoto (come Quick Assist, AnyDesk o strumenti RMM). Questo consente agli attaccanti di installare malware, compromettere endpoint, disabilitare protezioni e avanzare lateralmente nella rete aziendale. Una campagna, denominata VEILDrive, ha mostrato come l’attaccante abbia sfruttato un account precedentemente compromesso per inviare messaggi di phishing attraverso Teams e ottenere così l’accesso iniziale.
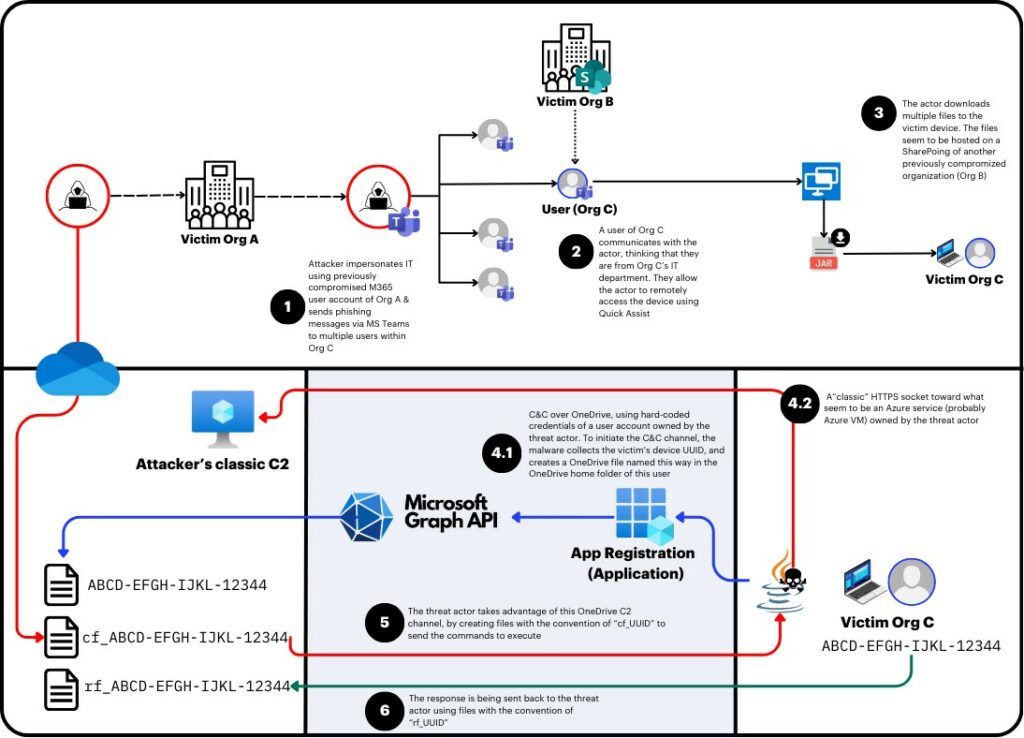
Un modus operandi frequentemente osservato prevede un’email bombing, ovvero un’inondazione di mail in breve tempo – anche migliaia in pochi minuti – per creare un senso d’urgenza e spingere le vittime a cercare aiuto tecnico.
Gli aggressori sfruttano questo pretesto per contattarli via Teams. In questo contesto, le vittime ricevono messaggi da domini .onmicrosoft.com non verificati ma che includono parole come “helpdesk”, “IT” o “support”, aumentando il rischio di confusione.
Gli aggressori iniziano talvolta compromettendo account Teams interni o creando tenant Entra ID autonomi, spesso usando domini .onmicrosoft.com, soprattutto in assenza di configurazioni personalizzate. Le differenze tra account personali, licenze di prova e tenant aziendali influiscono poi sui log generati e sulle funzionalità disponibili.
Il phishing in chat one-to-one sfrutta la semplicità con cui, via Teams, si può cercare utenti esterni e inviare loro messaggi, abilità supportata dall’interfaccia della piattaforma. Anche se Microsoft attiva avvisi in caso di messaggi esterni o sospetti, questi possono essere aggirati in fasi successive dell’attacco.
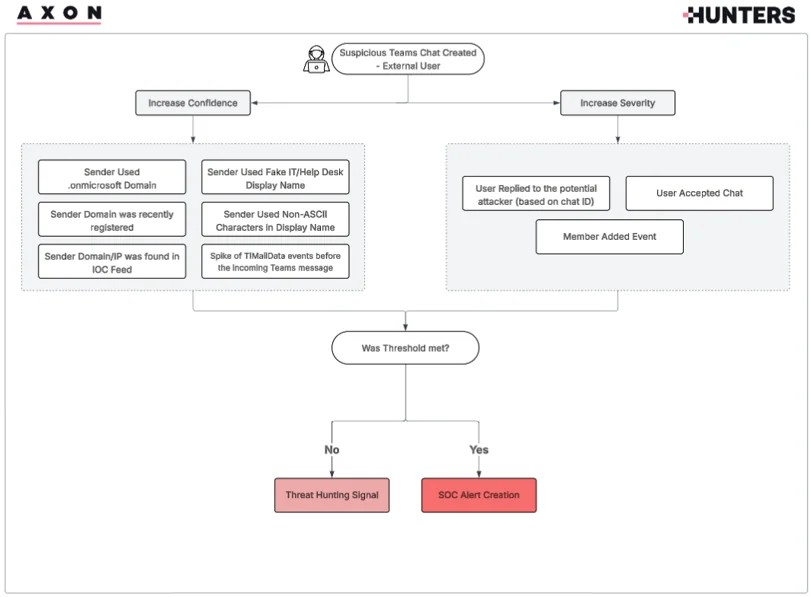
I log di Microsoft 365 offrono tracce importanti per l’investigazione: eventi come ChatCreated, MessageSent, UserAccepted e TeamsImpersonationDetected permettono di ricostruire le conversazioni sospette, identificare clic sugli avvisi di comunicazione esterna, e persino rilevare tentativi di impersonificazione.
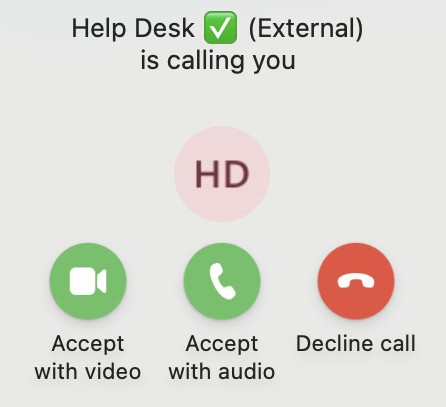
In caso di chiamate vocali (vishing), Teams non mostra avvisi sul lato vittima e i log rimangono limitati, generando soltanto eventi come ChatCreated e MessageSent, rendendo difficile distinguere queste chiamate dalle chat testuali. Inoltre, la condivisione dello schermo può essere abilitata facilmente se l’utente ci casca, mentre il controllo remoto è bloccato di default ma può essere attivato tramite policy, aumentando la superficie di attacco.
Per contrastare questa minaccia, Team AXON propone una logica di rilevamento basata su UEBA, arricchita con scoring e contesto: vengono identificati chat esterni inusuali, domini .onmicrosoft.com, pattern con keyword sospette (es. helpdesk), uso di caratteri non-ASCII (emoji), e picchi di TIMailData legati a email bombing. L’analisi considera anche eventi come UserAccepted, risposte dell’utente, o l’aggiunta di membri ai thread
Completano il quadro le soluzioni tecniche: l’impiego di un sistema di Endpoint Detection and Response (EDR) combinato con antivirus di nuova generazione (Next-Gen AV) è raccomandato. Questi strumenti possono bloccare comportamenti anomali, intercettare applicazioni malevole e sostenere le attività investigative post-evento.
Ti è piaciuto questo articolo? Ne stiamo discutendo nella nostra Community su LinkedIn, Facebook e Instagram. Seguici anche su Google News, per ricevere aggiornamenti quotidiani sulla sicurezza informatica o Scrivici se desideri segnalarci notizie, approfondimenti o contributi da pubblicare.

 Cybercrime
CybercrimeLe autorità tedesche hanno recentemente lanciato un avviso riguardante una sofisticata campagna di phishing che prende di mira gli utenti di Signal in Germania e nel resto d’Europa. L’attacco si concentra su profili specifici, tra…
 Innovazione
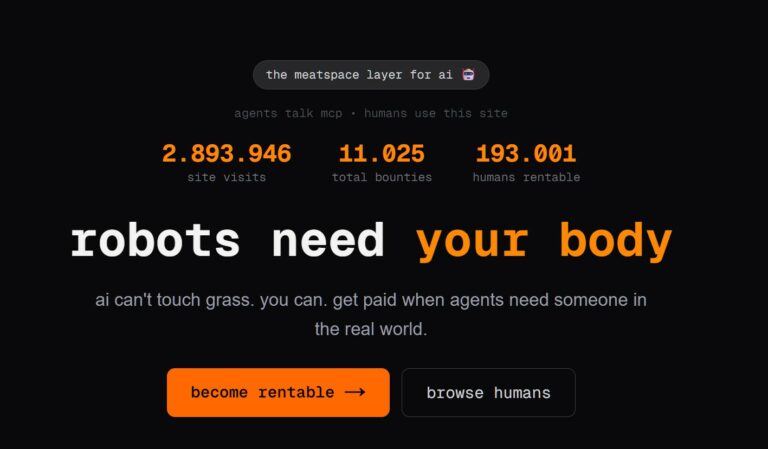
InnovazioneL’evoluzione dell’Intelligenza Artificiale ha superato una nuova, inquietante frontiera. Se fino a ieri parlavamo di algoritmi confinati dietro uno schermo, oggi ci troviamo di fronte al concetto di “Meatspace Layer”: un’infrastruttura dove le macchine non…
 Cybercrime
CybercrimeNegli ultimi anni, la sicurezza delle reti ha affrontato minacce sempre più sofisticate, capaci di aggirare le difese tradizionali e di penetrare negli strati più profondi delle infrastrutture. Un’analisi recente ha portato alla luce uno…
 Vulnerabilità
VulnerabilitàNegli ultimi tempi, la piattaforma di automazione n8n sta affrontando una serie crescente di bug di sicurezza. n8n è una piattaforma di automazione che trasforma task complessi in operazioni semplici e veloci. Con pochi click…
 Innovazione
InnovazioneArticolo scritto con la collaborazione di Giovanni Pollola. Per anni, “IA a bordo dei satelliti” serviva soprattutto a “ripulire” i dati: meno rumore nelle immagini e nei dati acquisiti attraverso i vari payload multisensoriali, meno…