Crazyhunter: The Ransomware with the Three-Dimensional Data Annihilation System That Redefines Data Destruction
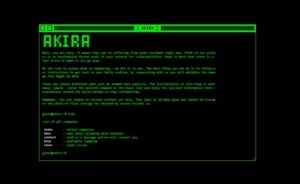
In the reconnaissance of the world of the underground and criminal groups carried out by Red Hot Cyber’s DarkLab threat intelligence lab, we came across a Data Leak Site of a cyber gang that had never been monitored before: Crazyhunter. With a distinct identity and a manifesto that sets it apart from other cybercriminal actors, Crazyhunter presents itself as a sophisticated operation that focuses on attack speed, data destruction, and a highly structured criminal branding system. From the information gathered on their Data Leak Site (DLS), accessible through the Tor network, the group appears to adopt a methodical and aggressive approach, aimed