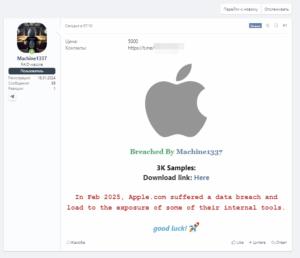
Apple in the crosshairs: alleged data breach of the Cupertino giant published on XSS
May 14, 2025 – In the early hours of this morning, an alarming post appeared on the Russian underground forum XSS , known to be a leading showcase for the buying and selling of compromised data: the Machine1337 group claimed responsibility for an alleged breach of Apple.com’s internal systems. The post, accompanied by the logo of the famous company and signed “Breached by Machine1337”, indicates that in February 2025 Apple would have been the victim of a data breach that would have led to the exposure of internal tools. According to what was declared by the malicious actor, 3,000 files were stolen, offered in samples with a download link. The entire package is put on