Akira Ransomware: The New Threat Using Webcams as Entry Points
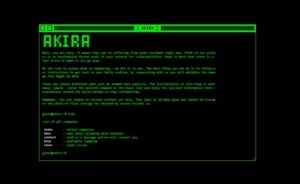
Akira represents one of the most recent ransomware threats capable of bypassing traditional organizational defense mechanisms. A recent case analyzed by the S-RM team highlighted how this group leveraged an unprotected webcam to deploy its payload, evading the defenses of an Endpoint Detection and Response (EDR) system. The Initial Modus Operandi The attack began with the compromise of the victim’s network through an internet-exposed remote access solution. Once inside, Akira deployed AnyDesk.exe, a remote management tool, to maintain control over the environment and proceed with data exfiltration. During the later stages of the attack, the attackers used the Remote Desktop Protocol (RDP)