FABRICKED: AMD Cloud Security Flaw Exposed, Is Your Data Safe?
Cloud servers that promise complete data protection are not as impenetrable as they seem. Researchers have found a way to bypass one of the main security technologies of AMD processors, without needin...
Frontier AI for Defenders: CrowdStrike and OpenAI TAC
CrowdStrike has been selected for OpenAI’sTrusted Access for Cyber (TAC) program. Today, OpenAI releasedGPT-5.4-Cyber, a frontier model designed for defensive cybersecurity, and expanded the TAC progr...
AI and Security: Is the Mythos Model a Breakthrough or Just Hype? Marcus Hutchins’s Vision
With the boom in artificial intelligence, bold claims about breakthroughs in cybersecurity are becoming increasingly common, but not all experts are willing to accept them at face value. A new controv...
Harvest Now, Decrypt Later: risks to your data in the near future
The Harvest Now, Decrypt Later (HNDL) model describes an attack strategy where encrypted data is collected today – despite being indecipherable – to decrypt in future when powerful quantum computers a...
From CVSS 9.8 to 7.0: What Happened to the Telegram Bug?
Yesterday, a critical vulnerability affecting the Telegram messenger was reported in the registry of the Zero Day Initiative (ZDI), identified as ZDI-CAN-30207. The issue was discovered by Michael DeP...
Just one Telegram sticker can hack you: the critical 9.8 RCE vulnerability still has no patch
There is something deeply unsettling about this vulnerability: no click is required, nothing needs to be opened. Simply receiving the content is enough. Researchers from the Trend Micro Zero Day Initi...
The Click War: Pornhub and the Global Standoff Over Age Verification
The digital landscape is undergoing a radical transformation, pitting adult industry titans against national regulators. At the heart of this dispute is not the content itself, but the gateway to it. ...
Xi Jinping and the Chinese APT’s Ambition
The post-COVID macro political movements, including ongoing conflicts, have prompted a majority of states to shift their medium- to long-term political objectives. Clearly, a paradigm shift has been v...
State-Sponsored “ILovePoop” Toolkit Targets Global Giants via React2Shell Vulnerability
The shelf life of a critical vulnerability is often measured in days, but React2Shell is proving to have a terrifyingly long tail. Months after its initial discovery, the flaw residing in React’s serv...
2149 BREAK THE SPHERE! The RHC & Hack The Box CTF at the RHC Conference 2026
In 2149, the world is no longer divided into nations, but into mega Autonomous City-States, hyper-technological urban giants competing for resources, data, and geopolitical power while the entire worl...
Latest news
Apple and Google under pressure: German regulator wants to remove DeepSeek
A former Australian university student has been accused of hacking Western Sydney University
Skynet is coming: the malware that attacks Artificial Intelligence!
Critical Vulnerabilities Discovered in Hundreds of Brother and Other Printers
He died because of ransomware! Another victim joins the list
A new fileless infostealer is being spread by Telegram and legitimate services
Citrix: New Critical Vulnerability from 9.2 Affects NetScaler – Attacks Underway!
REvil: Sentenced but then set free. The most controversial court case ever
Shock in France: the gentlemen of BreachForums were twenty-year-old French citizens!
Zero-Click Attack on Notepad++. HackerHood Tested the Exploit and It Really Works with Little
22,000 Sites At Risk: New Motors WordPress Vulnerability Allows Total Hacking
Qilin & Associates Law Firm: Ransomware Hires Lawyers, Launches “Intimidation Package”
HoneyPLC: the new honeypot that revolutionizes the defense of industrial plants
Redazione RHC - July 2nd, 2025
Discovering Predatory Sparrow: Identity, Goals, and Digital Arsenal of the Mysterious Threat Actor
Sandro Sana - July 1st, 2025
Famous hackers: the sad story of Jonathan James, aka c0mrade.
Silvia Felici - July 1st, 2025
Famous Hackers: The Story of Gary McKinnon.
Silvia Felici - July 1st, 2025
DuckDuckGo Updates Scam Blocker: Say Goodbye to Online Scams and Fake Sites!
Redazione RHC - July 1st, 2025
Cyberattacks on NFC contactless payments increase, new global threat
Redazione RHC - June 30th, 2025
The Race to 0day! China Advances in Offensive Cyberpower, While the US Is Forced to Chase
Agostino Pellegrino - June 30th, 2025
Cyberbullying and Digital Terror: Why Betti’s Comic Makes You Feel Uncomfortable (and That’s a Good Thing)
Andrea Gioia Lomoro - June 29th, 2025
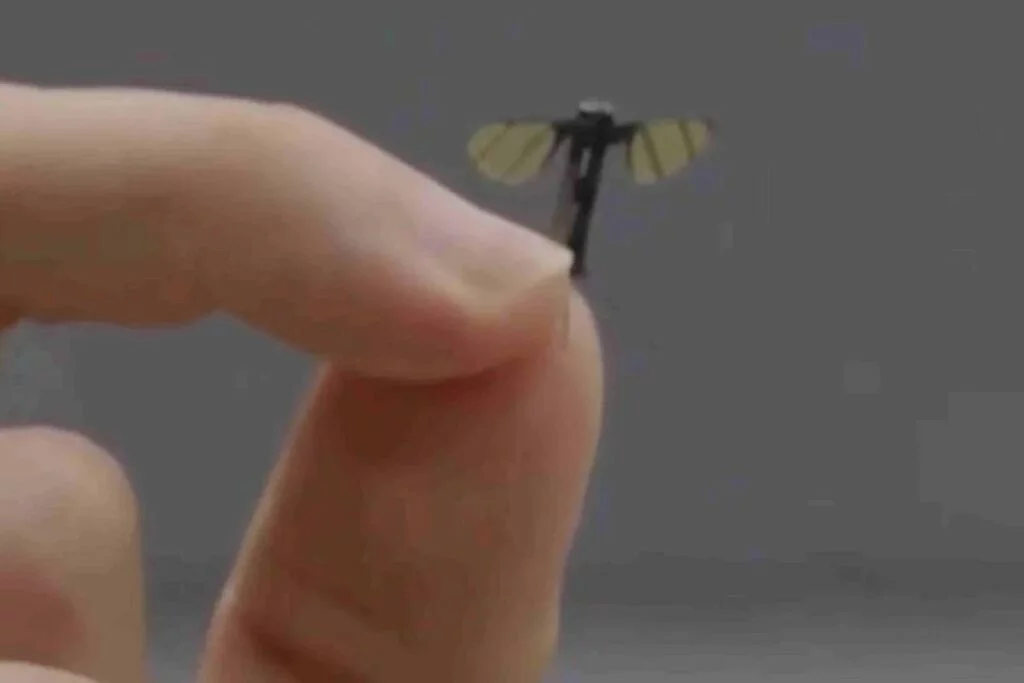
Miniaturized Military Drone, Mosquito-Sized Model Arrives and China Offers It
Redazione RHC - June 29th, 2025
Cyber Security: CISA and NSA Recommend Secure Programming Languages
Massimiliano Brolli - June 28th, 2025
Discover the latest critical CVEs issued and stay updated on the most recent vulnerabilities. Or search for a specific CVE