
Il Cybersecurity and Infrastructure Security Agency (CISA), ha ampliato la lista delle vulnerabilità sfruttate (KEV), segnalando una nuova vulnerabilità che interessa OpenPLC ScadaBR, a causa di indizi di sfruttamento attivi in corso.
USi tratta della falla di sicurezza, identificata come CVE-2021-26829 con un punteggio CVSS di 5,4, interessa le versioni del software su Windows e Linux, a causa di una vulnerabilità di cross-site scripting (XSS) nella pagina system_settings.shtm.
Poco più di un mese dopo la segnalazione di Forescout riguardo alla scoperta di un gruppo di hacktivisti filo-russi, noto come TwoNet, che aveva preso di mira il suo honeypot nel settembre 2025, scambiandolo per un impianto di trattamento delle acque, il difetto di sicurezza è stato aggiunto al catalogo KEV.
Le versioni interessate comprendono:
“L’aggressore non ha tentato di escalare i privilegi o di sfruttare l’host sottostante, concentrandosi esclusivamente sul livello dell’applicazione web dell’HMI”, ha affermato Forescout.
Come riportano i ricercatori, il gruppo TwoNet ha iniziato le sue operazioni su Telegram all’inizio di gennaio, concentrandosi inizialmente sugli attacchi DDoS (Distributed Denial of Service), prima di passare a una serie più ampia di attività, tra cui il targeting di sistemi industriali, il doxxing e offerte commerciali come il ransomware-as-a-service (RaaS), l’hack-for-hire e l’intermediazione di accesso iniziale.
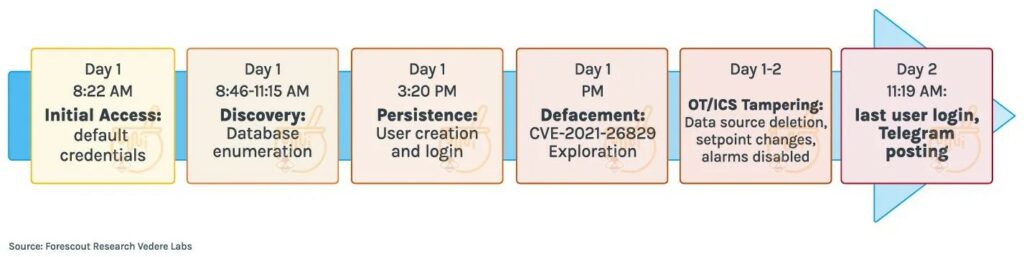
Il processo di distribuzione dell’impianto esca ha rivelato che l’autore dell’attacco ha impiegato circa 26 ore per passare dalla fase di accesso iniziale a quella di azione dirompente. In questo lasso di tempo, ha sfruttato credenziali predefinite per guadagnare l’accesso iniziale al sistema. Successivamente, ha condotto attività di ricognizione e instaurato la persistenza, tra le altre azioni, creando un nuovo account utente di nome “BARLATI“.
I malfattori hanno sfruttato la vulnerabilità CVE-2021-26829 per alterare la descrizione della pagina di accesso dell’HMI e visualizzare un messaggio pop-up “Hacked by Barlati”, inoltre hanno modificato le impostazioni di sistema in modo da disabilitare i registri e gli allarmi, senza rendersi conto di stare violando un sistema honeypot.
Si è scoperto che i tentativi di sfruttamento provengono dall’infrastruttura Google Cloud con sede negli Stati Uniti, il che dimostra come i malintenzionati stiano utilizzando come armi i servizi Internet legittimi per eludere il rilevamento e confondersi con il normale traffico di rete.
“Abbiamo osservato circa 1.400 tentativi di exploit che hanno interessato più di 200 CVE collegati a questa infrastruttura”, ha affermato Jacob Baines, CTO di VulnCheck . “Sebbene la maggior parte dell’attività assomigliasse ai template standard di Nuclei, le scelte di hosting, i payload e il targeting regionale dell’aggressore non erano in linea con il tipico utilizzo di OAST.”
Ti è piaciuto questo articolo? Ne stiamo discutendo nella nostra Community su LinkedIn, Facebook e Instagram. Seguici anche su Google News, per ricevere aggiornamenti quotidiani sulla sicurezza informatica o Scrivici se desideri segnalarci notizie, approfondimenti o contributi da pubblicare.
 Innovazione
InnovazioneL’evoluzione dell’Intelligenza Artificiale ha superato una nuova, inquietante frontiera. Se fino a ieri parlavamo di algoritmi confinati dietro uno schermo, oggi ci troviamo di fronte al concetto di “Meatspace Layer”: un’infrastruttura dove le macchine non…
 Cybercrime
CybercrimeNegli ultimi anni, la sicurezza delle reti ha affrontato minacce sempre più sofisticate, capaci di aggirare le difese tradizionali e di penetrare negli strati più profondi delle infrastrutture. Un’analisi recente ha portato alla luce uno…
 Vulnerabilità
VulnerabilitàNegli ultimi tempi, la piattaforma di automazione n8n sta affrontando una serie crescente di bug di sicurezza. n8n è una piattaforma di automazione che trasforma task complessi in operazioni semplici e veloci. Con pochi click…
 Innovazione
InnovazioneArticolo scritto con la collaborazione di Giovanni Pollola. Per anni, “IA a bordo dei satelliti” serviva soprattutto a “ripulire” i dati: meno rumore nelle immagini e nei dati acquisiti attraverso i vari payload multisensoriali, meno…
 Cyber Italia
Cyber ItaliaNegli ultimi giorni è stato segnalato un preoccupante aumento di truffe diffuse tramite WhatsApp dal CERT-AGID. I messaggi arrivano apparentemente da contatti conosciuti e richiedono urgentemente denaro, spesso per emergenze come spese mediche improvvise. La…