Red Hot Cyber - Notizie su Cybercrime e Sicurezza Informatica
Aperti i battenti del primo negozio di robot umanoidi al mondo in Cina. Saremo pronti?
Alle dieci del mattino, a Wuhan, due robot umanoidi alti 1,3 metri iniziano a muoversi con precisione. Girano, saltano, seguono il ritmo. È il segnale di apertura del primo negozio 7S di robot umanoid...
Azienda automotive italiana nel mirino degli hacker: in vendita l’accesso per 5.000 dollari
Il 29 gennaio 2026, sul forum BreachForums, l’utente p0ppin ha pubblicato un annuncio di vendita relativo a un presunto accesso amministrativo non autorizzato ai sistemi interni di una “Italian Car Co...
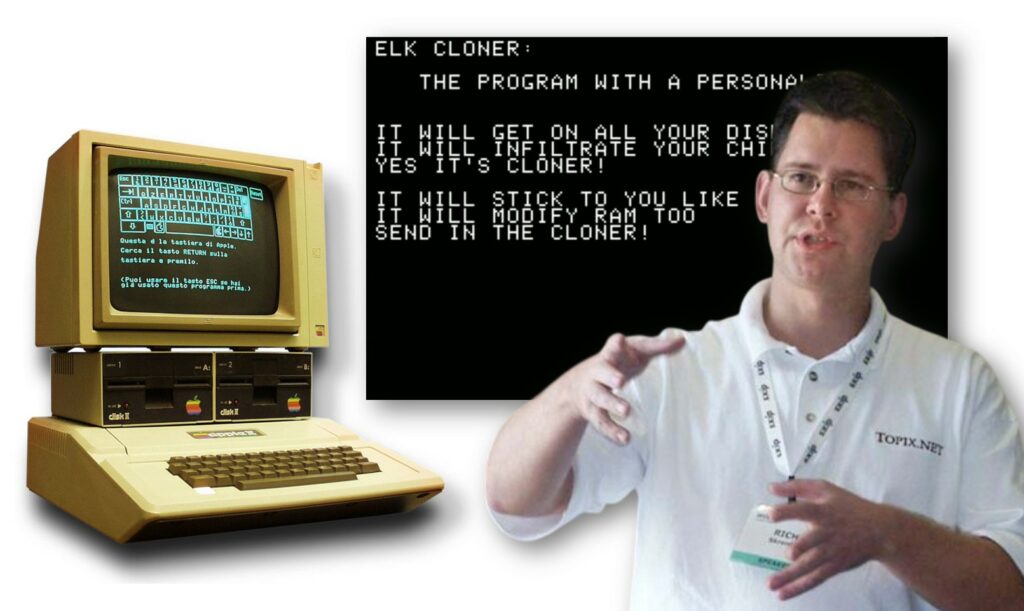
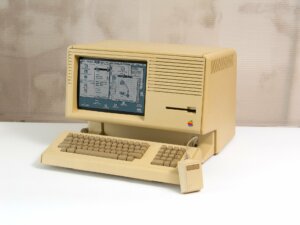
Elk Cloner: Il primo virus informatico della storia nacque come uno scherzo
Alla fine degli anni 90, Internet era ancora piccolo, lento e per pochi. In quel periodo, essere “smanettoni” significava avere una conoscenza tecnica che sembrava quasi magia agli occhi degli altri. ...
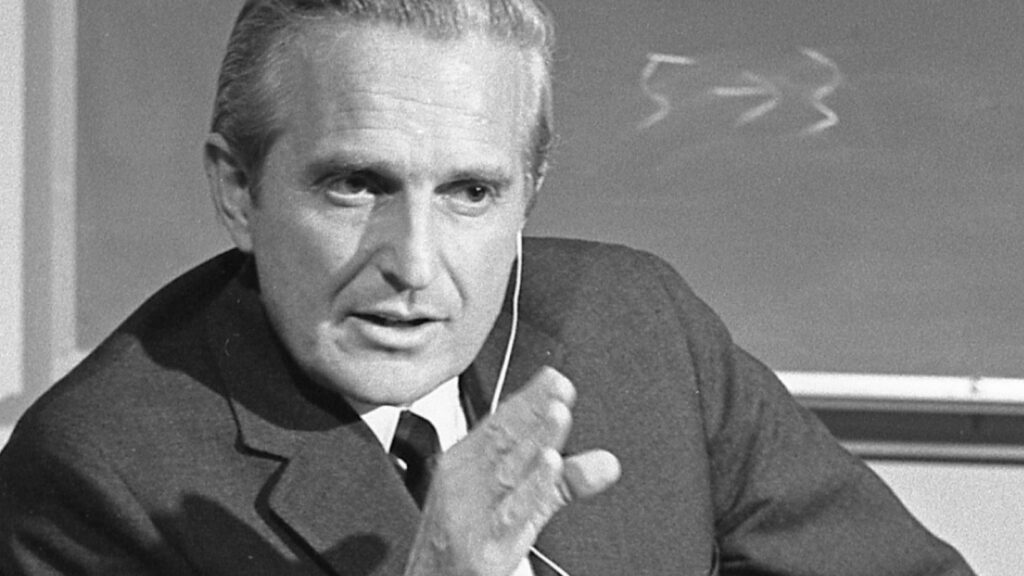
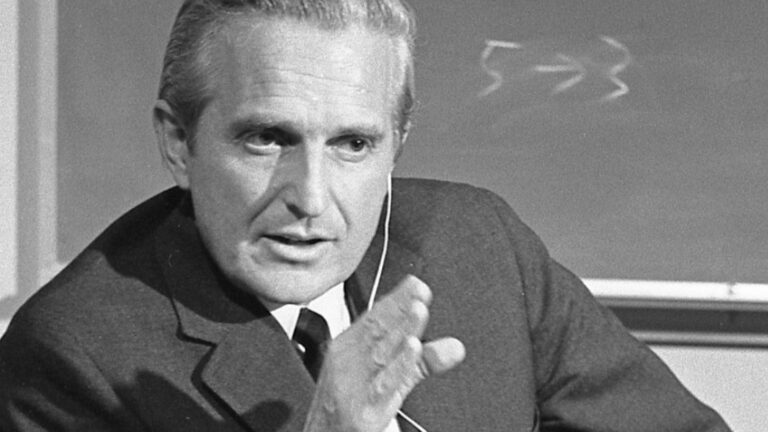
Oggi nasceva Douglas Engelbart: l’uomo che ha visto e inventato il futuro digitale
Certe volte, pensandoci bene, uno si chiede come facciamo a dare per scontato il mondo che ci circonda. Tipo, clicchiamo, scorriamo, digitiamo, e tutto sembra così naturale, quasi fosse sempre stato q...
L’IA non chiede il permesso: sta riscrivendo le regole in fretta e probabilmente male
L’intelligenza artificiale è entrata nel lavoro senza bussare. Non come una rivoluzione urlata, ma come una presenza costante, quasi banale a forza di ripetersi. Ha cambiato il modo in cui le persone ...
Attenzione al “I am not a robot”: la trappola malware che usa Google Calendar
Una nuova minaccia si aggira, usando la nostra più grande debolezza: l’abitudine. Quante volte, infatti, capita di ritrovarsi a cliccare su caselle di verifica senza pensarci due volte? Ora, pare che ...
WinRAR come arma: Google scopre una falla sfruttata da APT e cybercriminali
La falla di sicurezza in WinRAR, emersa durante la scorsa estate, ha mostrato una diffusione maggiore rispetto alle aspettative. Diverse organizzazioni, sia criminali comuni che gruppi APT finanziati ...
Colpo al cuore del cybercrime: RAMP messo offline. Il “tempio” del ransomware cade!
Il forum RAMP (Russian Anonymous Marketplace), uno dei principali punti di riferimento del cybercrime underground internazionale, è stato ufficialmente chiuso e sequestrato dalle forze dell’ordine sta...
La privacy è morta? No, ma è in coma! Cosa celebriamo davvero oggi 28 gennaio
Oggi è il 28 gennaio e, come ogni anno da un bel po’ di tempo a questa parte, ci ritroviamo a celebrare la Giornata europea della protezione dei dati. È una roba che nasce nel 2006, o giù di lì, per r...
OpenSSL: 12 bug di sicurezza rilevati tra i quali una vulnerabilità critica
Un aggiornamento di sicurezza è stato rilasciato dai responsabili della manutenzione di OpenSSL, la libreria crittografica, al fine di risolvere circa una dozzina di vulnerabilità che includono, tra g...
Articoli più letti dei nostri esperti
Aperti i battenti del primo negozio di robot umanoidi al mondo in Cina. Saremo pronti?
Carolina Vivianti - 30 Gennaio 2026
Azienda automotive italiana nel mirino degli hacker: in vendita l’accesso per 5.000 dollari
Luca Stivali - 30 Gennaio 2026
Ivanti corre ai ripari: falle zero-day colpiscono l’Endpoint Manager Mobile
Redazione RHC - 30 Gennaio 2026
Photoshop ora gira su Linux. Un Hacker lo ha fatto ed è finalmente speranza
Silvia Felici - 30 Gennaio 2026
Il codice non mente: i legami segreti tra i gruppi hacker HoneyMyte e Mustang Panda
Bajram Zeqiri - 30 Gennaio 2026
Vulnerabilità da score 10 in Johnson Controls: gli edifici intelligenti sono a rischio
Redazione RHC - 30 Gennaio 2026
La Cina scommette sulle tecnologie quantistiche per la superiorità militare
Redazione RHC - 30 Gennaio 2026
Elk Cloner: Il primo virus informatico della storia nacque come uno scherzo
Silvia Felici - 30 Gennaio 2026
Oggi nasceva Douglas Engelbart: l’uomo che ha visto e inventato il futuro digitale
Massimiliano Brolli - 30 Gennaio 2026
BitLocker sotto accusa: Microsoft ammette di consegnare le chiavi di cifratura all’FBI
Redazione RHC - 29 Gennaio 2026
Ultime news
Aperti i battenti del primo negozio di robot umanoidi al mondo in Cina. Saremo pronti?
Azienda automotive italiana nel mirino degli hacker: in vendita l’accesso per 5.000 dollari
Ivanti corre ai ripari: falle zero-day colpiscono l’Endpoint Manager Mobile
Photoshop ora gira su Linux. Un Hacker lo ha fatto ed è finalmente speranza
Il codice non mente: i legami segreti tra i gruppi hacker HoneyMyte e Mustang Panda
Vulnerabilità da score 10 in Johnson Controls: gli edifici intelligenti sono a rischio
Scopri le ultime CVE critiche emesse e resta aggiornato sulle vulnerabilità più recenti. Oppure cerca una specifica CVE
Ricorrenze storiche dal mondo dell'informatica
Articoli in evidenza
 Innovazione
InnovazioneAlle dieci del mattino, a Wuhan, due robot umanoidi alti 1,3 metri iniziano a muoversi con precisione. Girano, saltano, seguono il ritmo. È il segnale di apertura del primo negozio 7S di robot umanoidi del…
 Cyber Italia
Cyber ItaliaIl 29 gennaio 2026, sul forum BreachForums, l’utente p0ppin ha pubblicato un annuncio di vendita relativo a un presunto accesso amministrativo non autorizzato ai sistemi interni di una “Italian Car Company”. Come spesso accade in questo tipo di annunci, nessun riferimento…
 Cyber News
Cyber NewsIvanti ha rilasciato una serie di aggiornamenti critici per arginare due vulnerabilità di sicurezza che hanno colpito Ivanti Endpoint Manager Mobile (EPMM). Si tratta di falle sfruttate attivamente in attacchi zero-day, una criticità tale da…
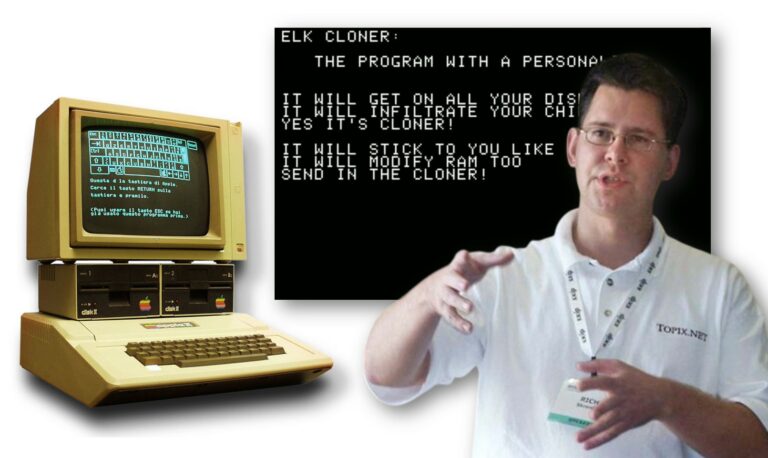 Cultura
CulturaAlla fine degli anni 90, Internet era ancora piccolo, lento e per pochi. In quel periodo, essere “smanettoni” significava avere una conoscenza tecnica che sembrava quasi magia agli occhi degli altri. Non era raro che…
 Cultura
CulturaCerte volte, pensandoci bene, uno si chiede come facciamo a dare per scontato il mondo che ci circonda. Tipo, clicchiamo, scorriamo, digitiamo, e tutto sembra così naturale, quasi fosse sempre stato qui. E invece no,…